Installing and Configuring Windows Server 2012 온라인 연습
최종 업데이트 시간: 2025년09월06일
당신은 온라인 연습 문제를 통해 Microsoft 70-410 시험지식에 대해 자신이 어떻게 알고 있는지 파악한 후 시험 참가 신청 여부를 결정할 수 있다.
시험을 100% 합격하고 시험 준비 시간을 35% 절약하기를 바라며 70-410 덤프 (최신 실제 시험 문제)를 사용 선택하여 현재 최신 497개의 시험 문제와 답을 포함하십시오.

정답: 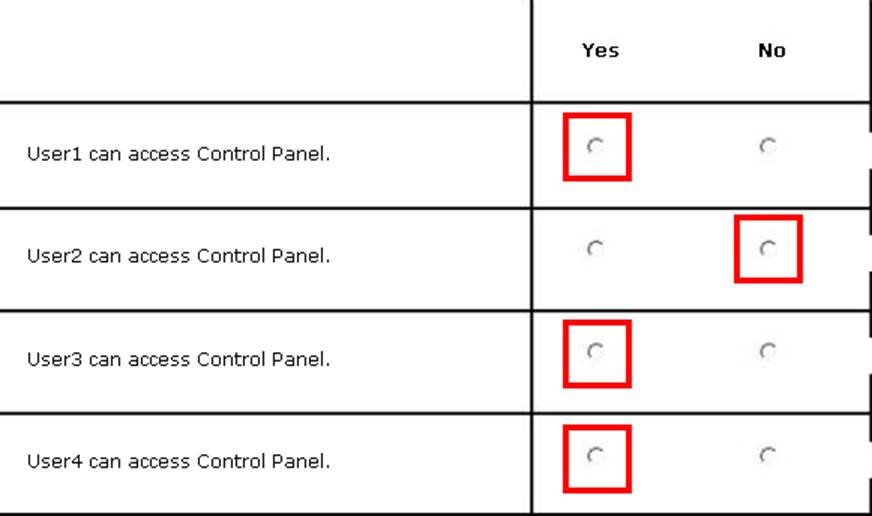
Explanation:
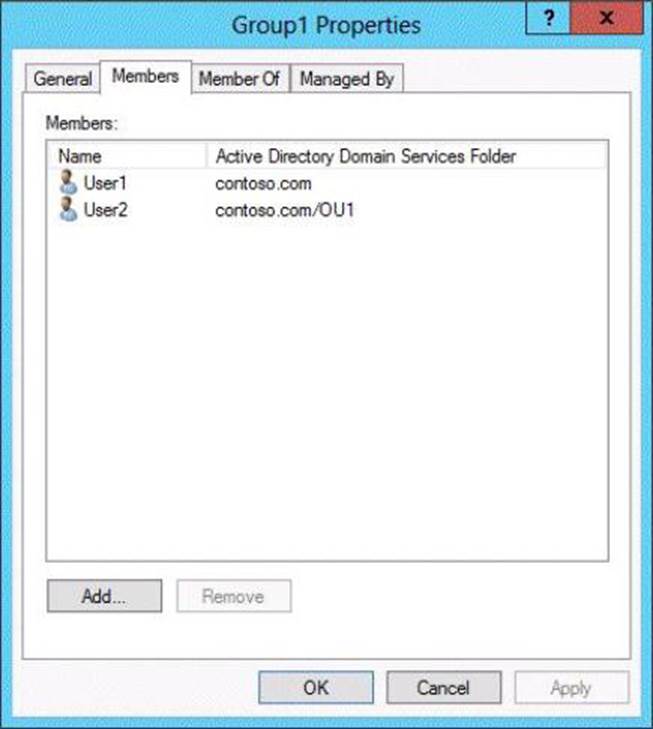
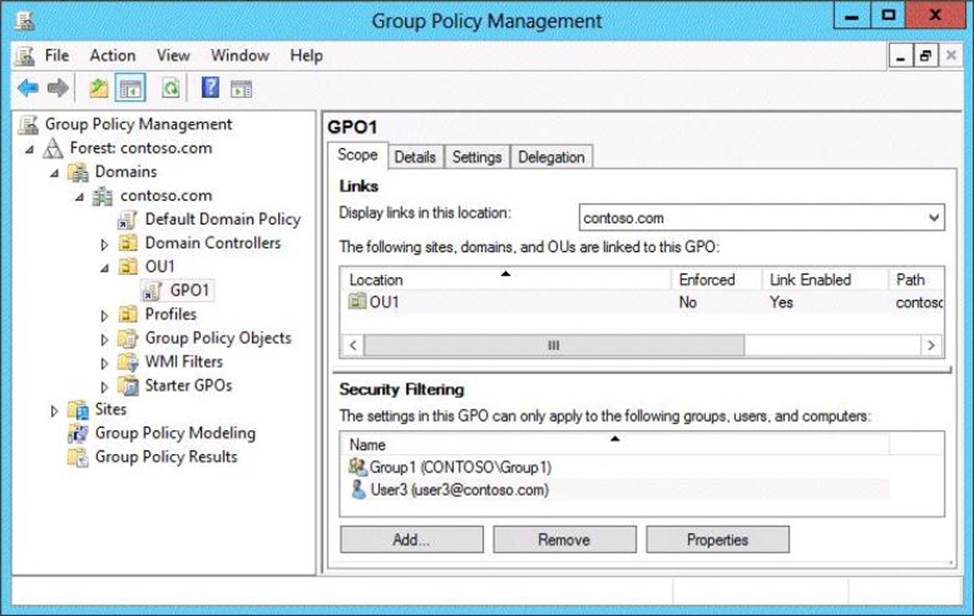
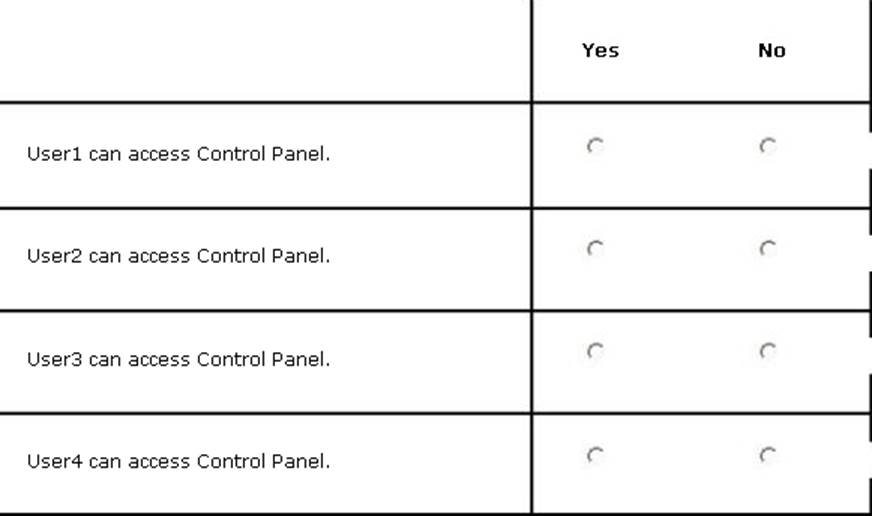
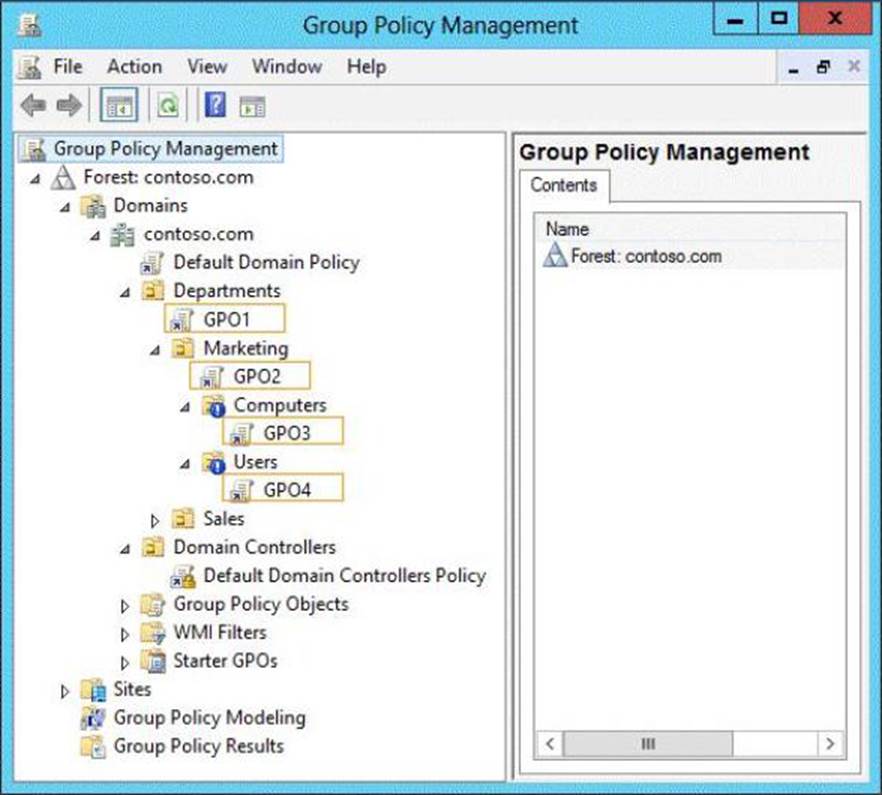
Group Policy does NOT APPLY TO SECURITY GROUPS, only users and computers in an OU. Consequently, the only users in the OU are User2 and User4. Since the Security Filtering specifies that the policy will only apply to users/computers in the OU who are members of Group1 or User3, User4 will not have the policy applied. Since User2 is, in fact, a member of Group1, the policy will be applied to user 2. Thus, the only user who will not be able to access the control panel is User2.
정답: 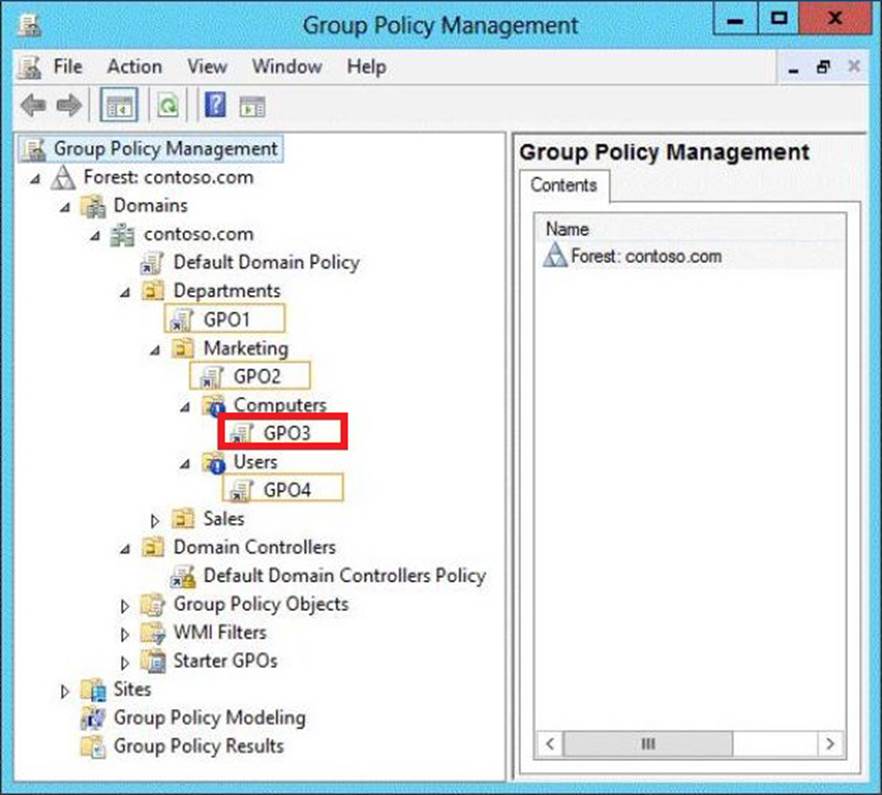
Explanation:
Application control policies specify which programs are allowed to run on the local computer and which are not.
References:
http://technet.microsoft.com/en-us/library/hh125923(v=ws.10).aspx
http://technet . microsoft .com /en-us/library/cc781458(v=WS . 10) . aspx
http://technet . microsoft .com /en-us/library/hh967461 . aspx
http://technet . microsoft .com /en-us/library/ee461050 . aspx
http://technet . microsoft .com /en-us/library/ee461044 . aspx
정답:
Explanation:
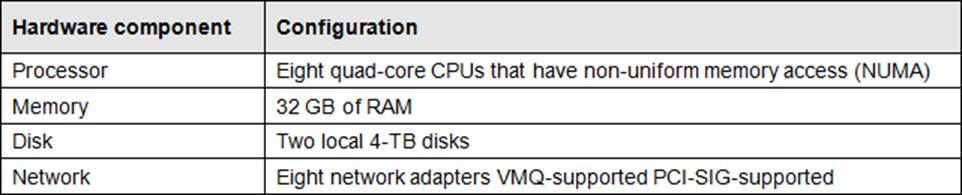
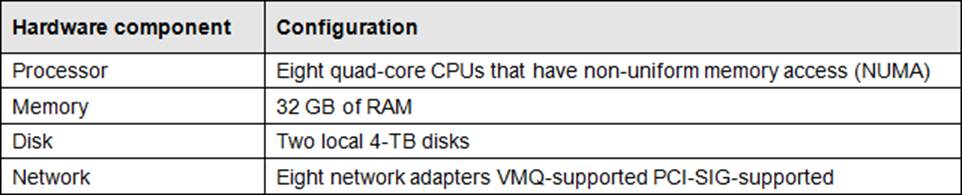
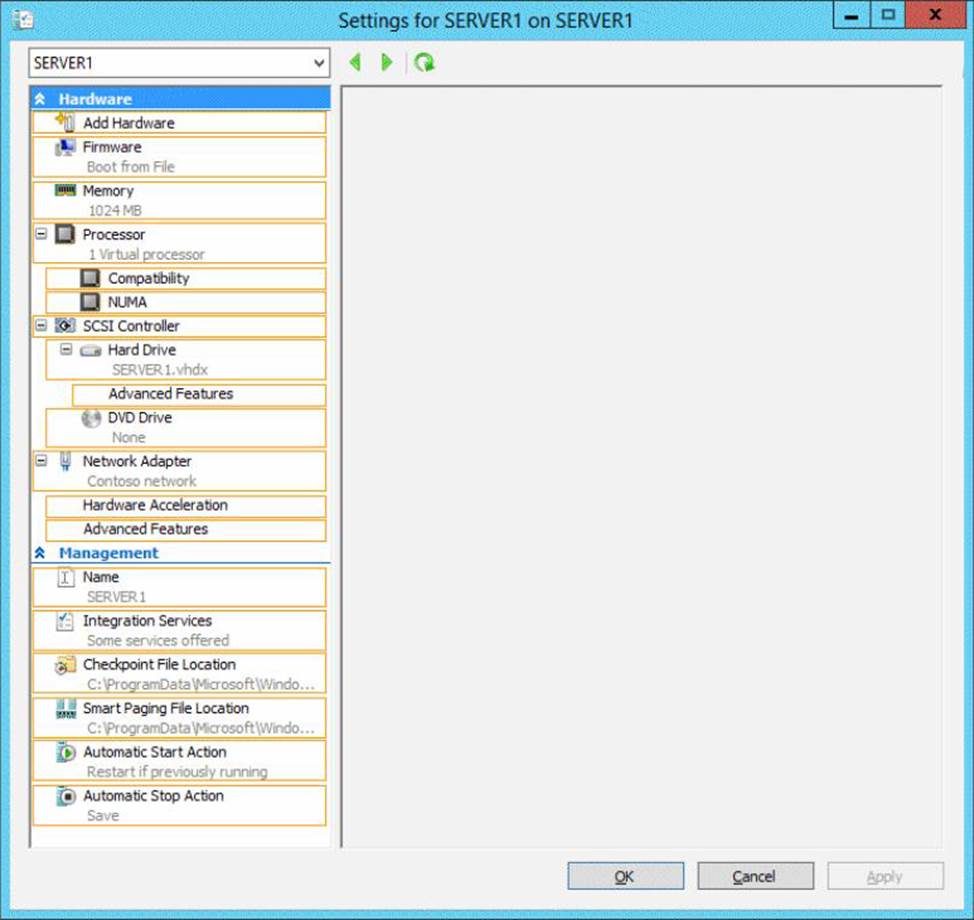
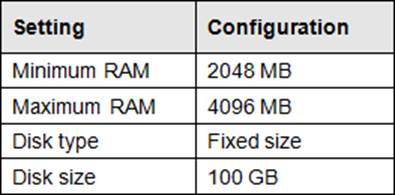
B. Resource controls provide you with several ways to control the way that Hyper-V allocates resources to virtual machine. Resource control in used in the event where you need to adjust the computing resources of a virtual machine, you can reconfigure the resources to meet the changing needs. You can also specify resource controls to automate how resources are allocated to virtual machines.
References:
http://technet.microsoft.com/en-us/library/cc766320(v=ws.10).aspx
http://technet.microsoft.com/en-us/library/hh831410.aspx
http://technet.microsoft.com/en-us/library/cc742470.aspx
Exam Ref 70-410, Installing and Configuring Windows Server 2012 R2, Chapter 3: Configure Hyper-V, Objective 3.1: Create and Configure virtual machine settings, p.144
Training Guide: Installing and Configuring Windows Server 2012 R2: Chapter 7: Hyper-V Virtualization, Lesson 2: Deploying and configuring virtual machines, p.335
정답:
Explanation:
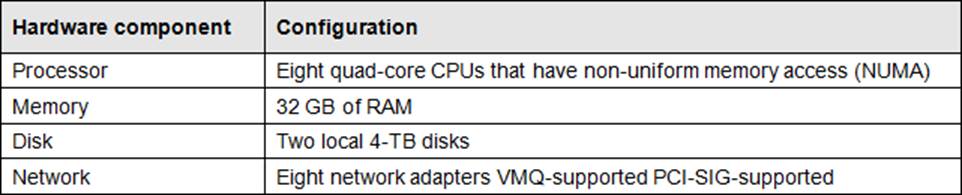
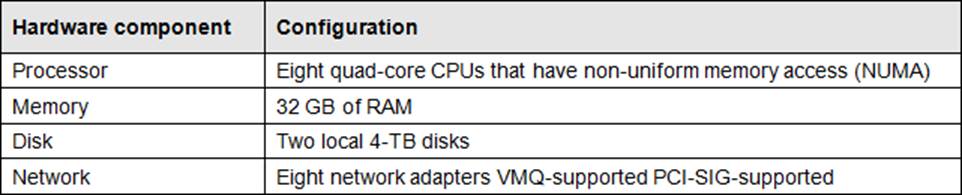
Single-root I/O virtualization -capable network adapters can be assigned directly to a virtual machine to maximize network throughput while minimizing network latency and the CPU overhead required for processing network traffic.
References: http://technet.microsoft.com/en-us/library/cc766320(v=ws.10).aspx
http://technet.microsoft.com/en-us/library/hh831410.aspx
Exam Ref 70-410, Installing and Configuring Windows Server 2012 R2, Chapter 3: Configure Hyper-V, Objective 3.1: Create and Configure virtual machine settings, p.144
Training Guide: Installing and Configuring Windows Server 2012 R2: Chapter 7: Hyper-V Virtualization, Lesson 2: Deploying and configuring virtual machines, p.335
정답:
Explanation:
The Integration Services settings on virtual machines include services such as operating system shutdown, time synchronization, data exchange, Heartbeat, and Backup (volume snapshot services). This snapshot will ensure that the state of VM1 is saved prior to backup.
References: http://msdn.microsoft.com/en-us/library/dd405549(v=vs.85).aspx
Exam Ref 70-410, Installing and Configuring Windows Server 2012 R2, Chapter 3: Configure Hyper-V, Objective 3.1: Create and Configure virtual machine settings, p.144
정답:
Explanation:
Configure the BIOS of the computer to enable PXE boot, and set the boot order so that it is booting from the network is first.
References: http://technet.microsoft.com/en-us/library/cc766320(v=ws.10).aspx
Exam Ref 70-410, Installing and Configuring Windows Server 2012 R2, Chapter 3: Configure Hyper-V, Objective 3.1: Create and Configure virtual machine settings, p.144
Training Guide: Installing and Configuring Windows Server 2012 R2: Chapter 7: Hyper-V Virtualization, Lesson 2: Deploying and configuring virtual machines, p.335
정답: 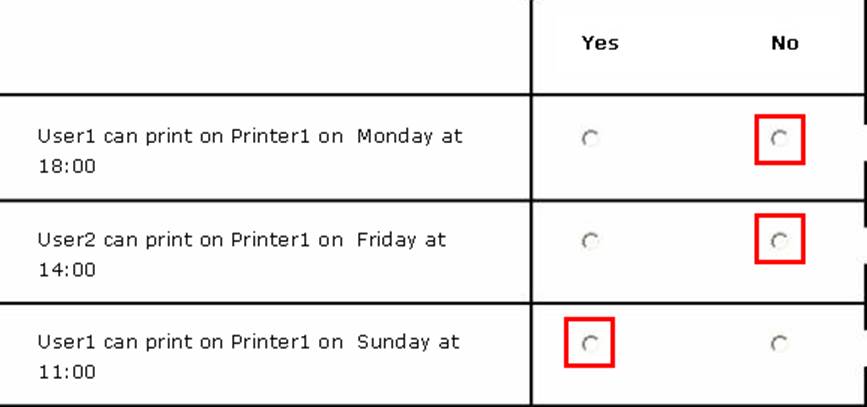
정답:
Explanation:
The LocalAccountTokenFilterPolicy setting affects how administrator credentials are applied to remotely administer the computer.
Reference: http://support.microsoft.com/kb/942817
정답:
Explanation:
Information regarding IPsec policy changes, etc. can be found in the Event Viewer. Thus you need to enable the NetFirewallRule command. This will allow you to view the event logs.
정답: 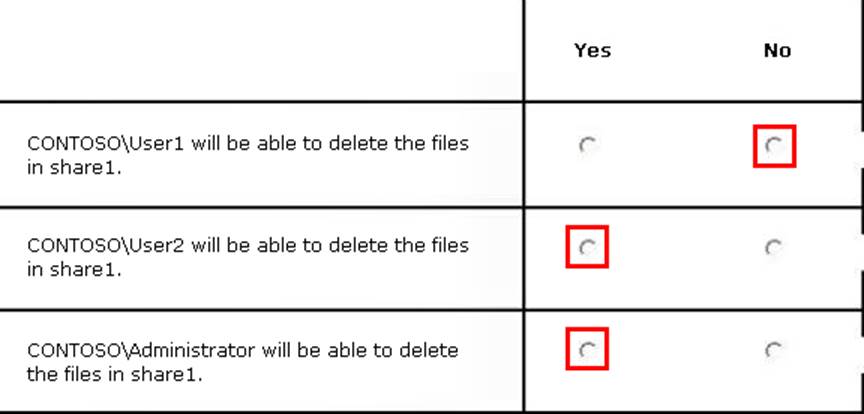
Explanation:
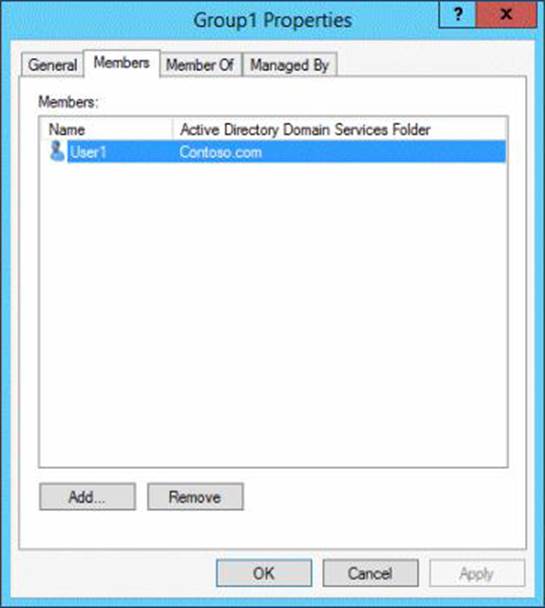
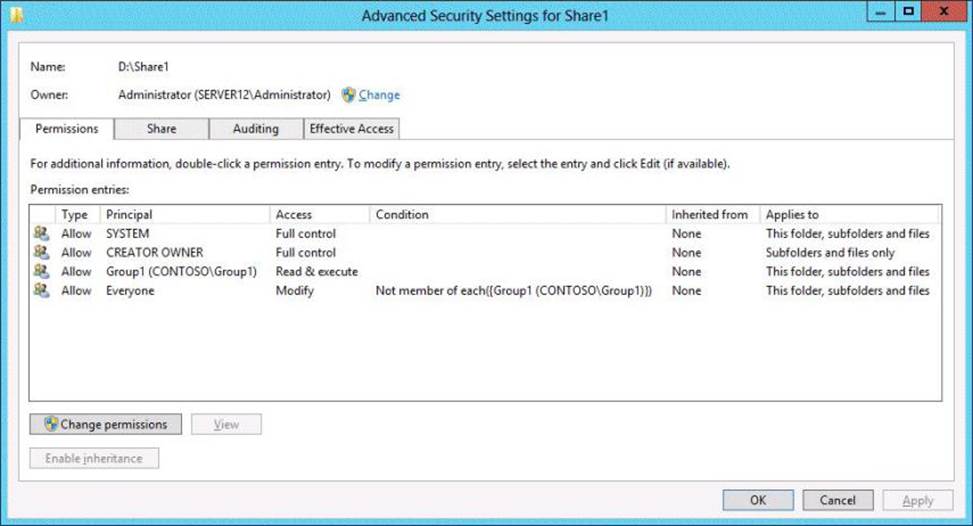
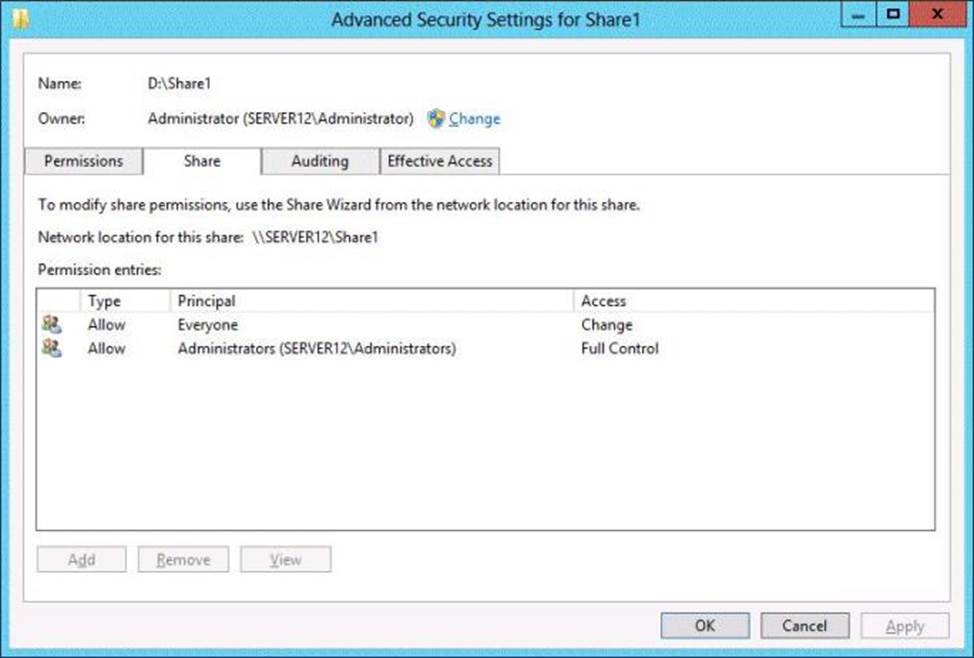
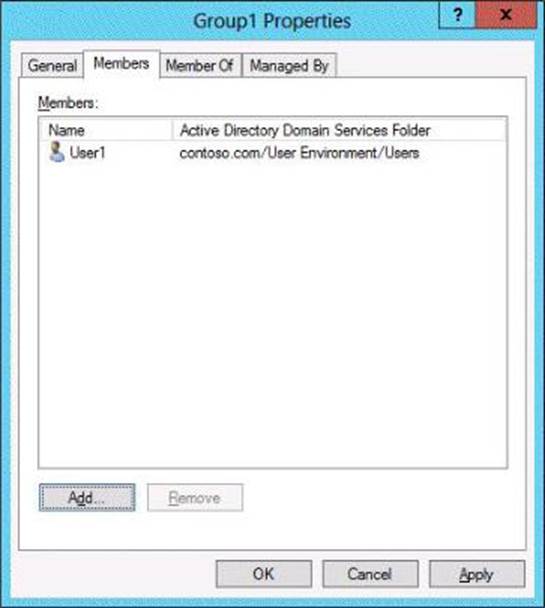
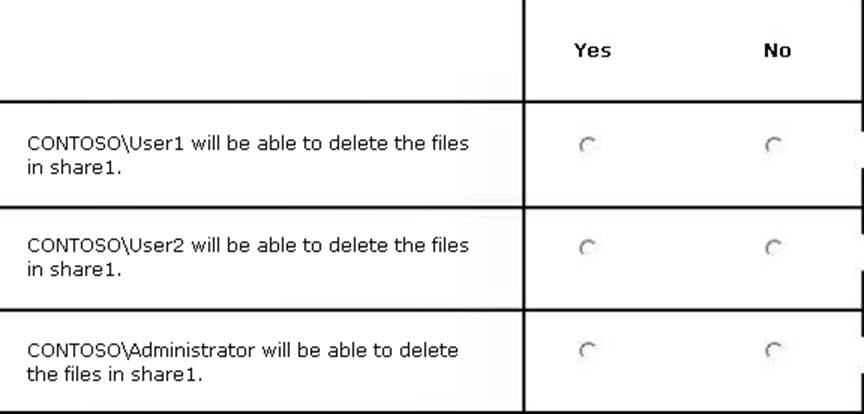
NTFS permissions control access to the files and folders stored on disk volumes formatted with the NTFS file system. Share permissions control access to folders over a network. To access a file over a network, a user must have appropriate share permissions (and appropriate NTFS permissions if the shared folder is on an NTFS volume). Granting a user Full Control NTFS permission on a folder enables that user to take ownership of the folder unless the user is restricted in some other way.User1 was not granted Full Control permission.
The Administrators have Full Control permission. I assume that User2 is an administrator since the Group1 exhibit shows only User1 as a member.
References: http://technet . microsoft .com /en-us/library/cc754178 . aspx
Exam Reference 70-410: Installing and configuring Windows Server 2012 R2, Chapter 2: Configure server roles and features, Objective 2.1: Configure file and share access, p.75-80
정답: 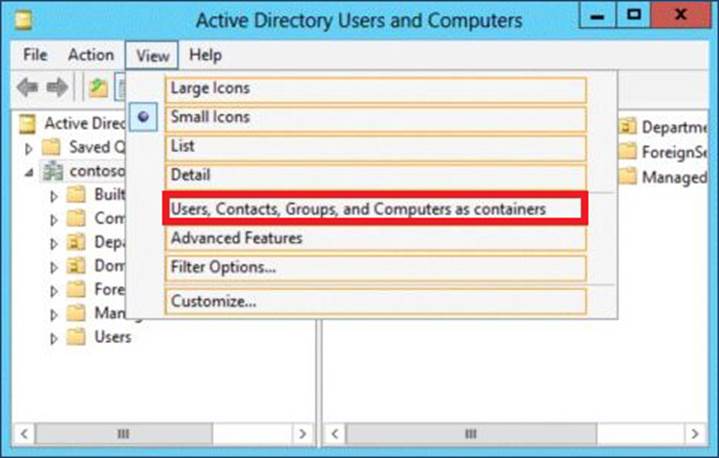
Explanation:
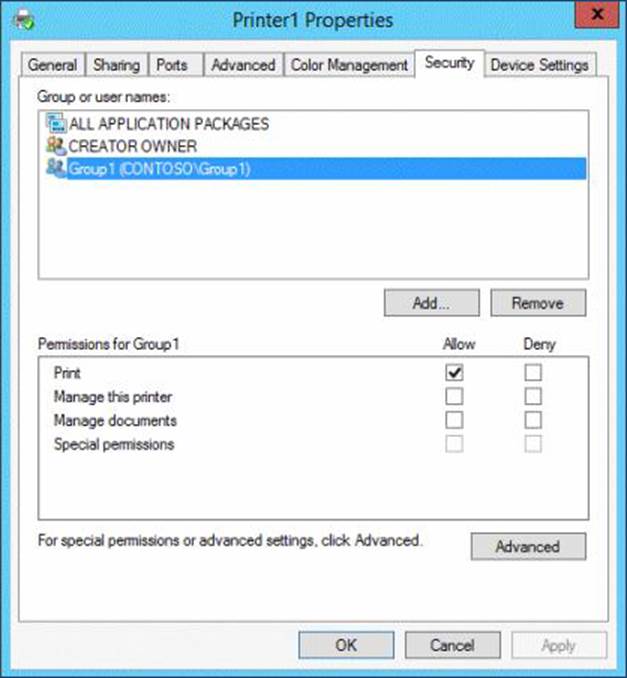
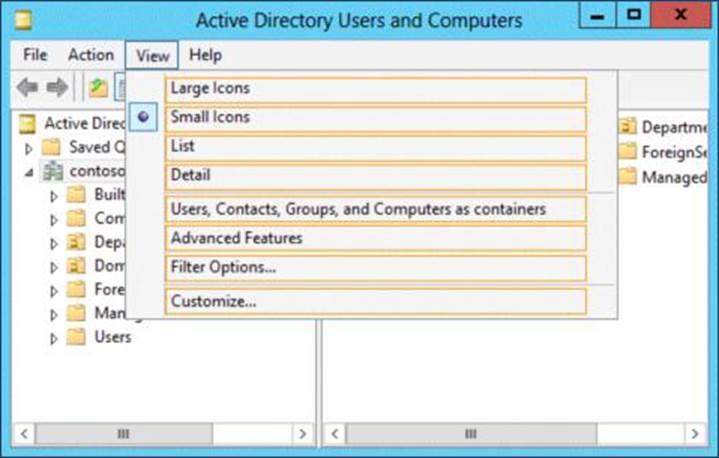
You can view printer objects in Active Directory by clicking Users, Groups, and Computers as containers from the View menu in the Active Directory Users and Computers snap-in. By default, printer objects are created under the machine object in which they are shared. After you turn on the Users, Groups, and Computers as containers option, you can see printers by expanding the printer's host computer.
Reference: http://support . microsoft .com /kb/235925
정답: 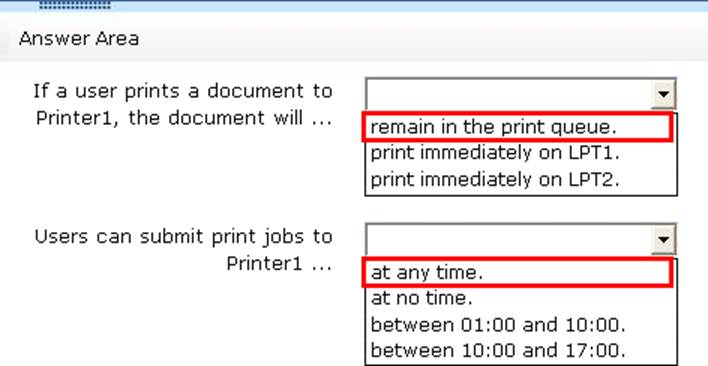
Explanation:
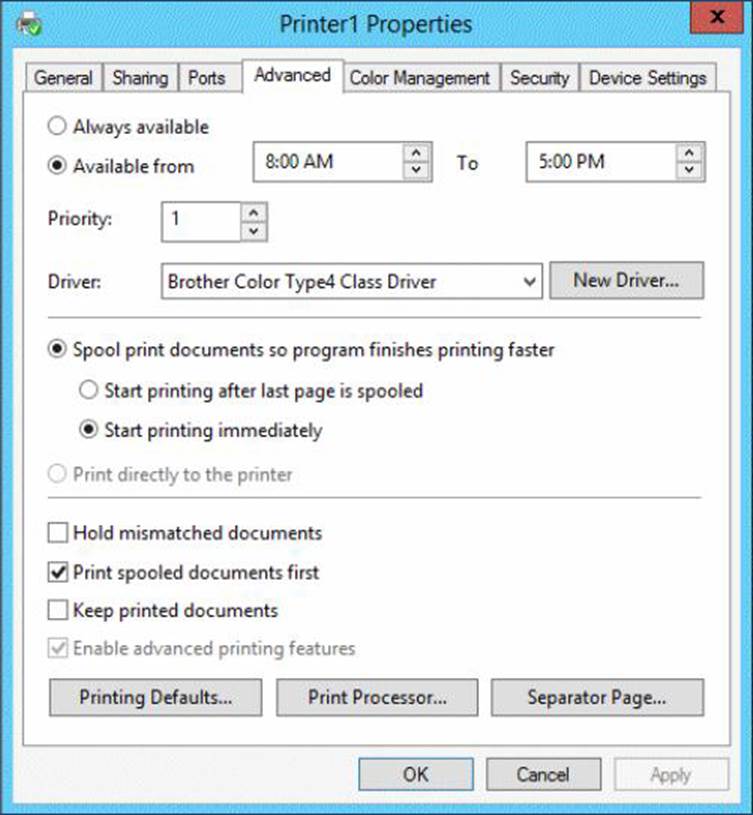
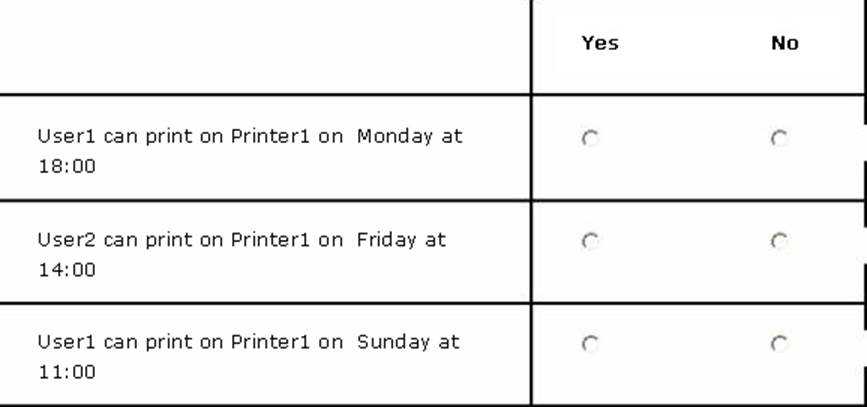
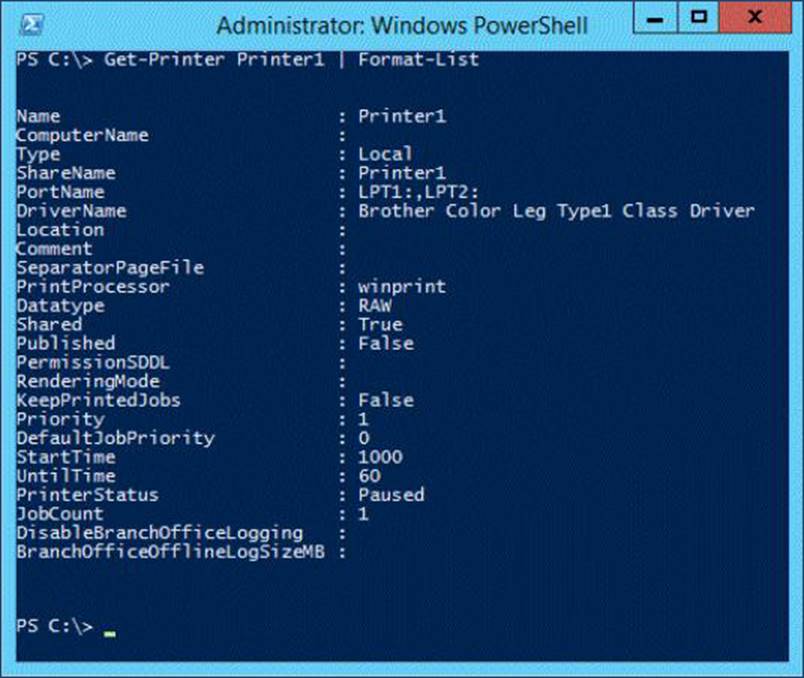
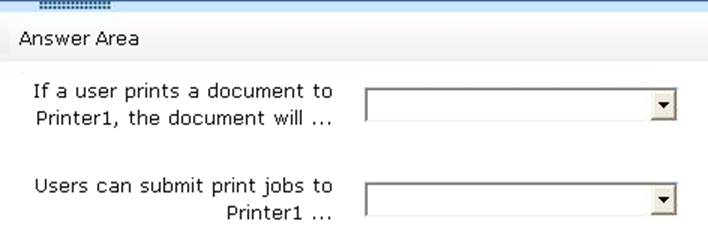
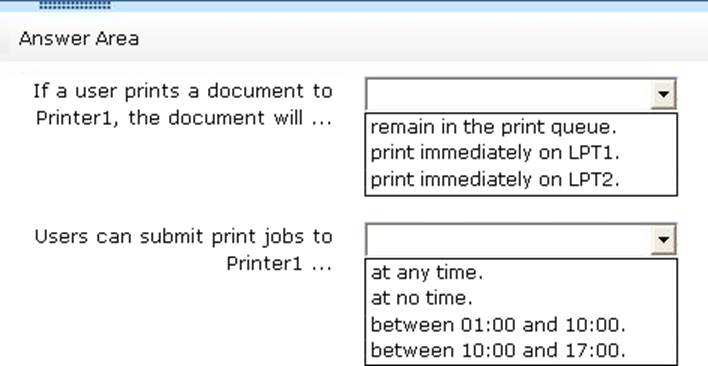
* The printer is paused.
* Jobs can always be permitted (even if the printer is paused, or printer not started).
Note:
StartTime
Date and time that a printer can start to print a job ― if the printer is limited to print at specific times. This value is expressed as the time elapsed since 12:00 AM GMT (Greenwich Mean Time).
This is sort of a trick question. As it stands, when the PowerShell script was executed, the printer is in "Paused" status, so any submitted job will go to the queue and remain there until the status is "Available". As for the ability to submit a job, a user can SUBMIT the job at any time. If it is outside of the printer's availability range, it will simply remain in the queue until the printer's start time is reached.
정답:
Explanation:
Windows spools print jobs by default to the following directory as they are processed:
%SystemRoot%\SYSTEM32\SPOOL\PRINTERS.
It is possible for the administrator of a Windows print server to manually instruct Windows the location for placing the spool files, if for example there is a concern for disk space.
정답: 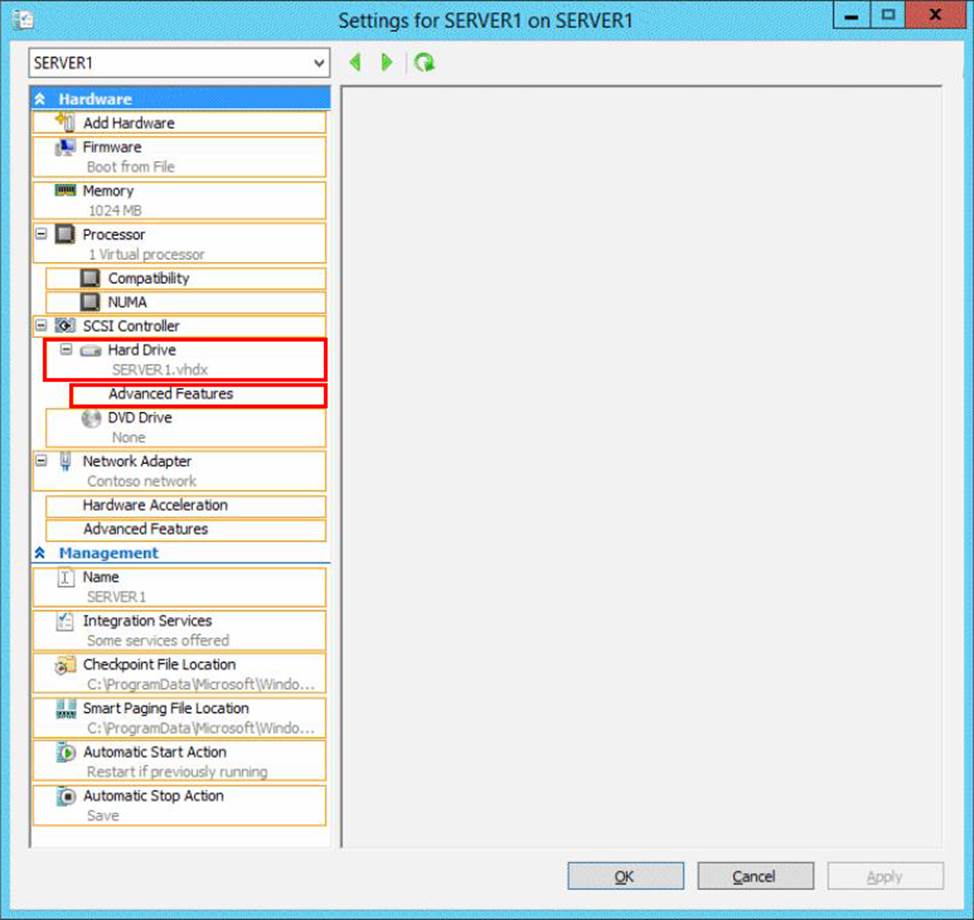
정답:
Explanation:
Changing between a fixed and dynamic disk type does not alter the size of a SNAPSHOT much at all.
However, since a snapshot is a record of a VMs state at the exact time that the snapshot was taken, shutting down the VM before taking the snapshot prevents the snapshot from having to contain all of the data in RAM (as there is no data in memory when a machine is powered down).
The question states that the solution should minimize the amount of disk space used for the checkpoint of VM1. If the checkpoint is taken while VM1 is running, there will be two attritional files present at the checkpoint location; a .VSV with VM1 saved state files and a .BIN file which contains VM1’s memory contents. If, however, VM1 is shut down first, these files will not be created, thus saving disk space.
In order to convert Disk1.vhd to a dynamically expanding disk, VM1 still have to be shut down.